Claude Mythos is too dangerous for public consumption...
Chapters5
Discusses the sensational claims about Mythos and the broad security and societal fears it provokes.
Fireship’s review of Mythos argues it's a dangerous leap in AI capability, but not necessarily a world-ending threat—yet its security implications and release strategy demand cautious scrutiny.
Summary
Fireship’s take on Mythos centers around its claim of immense power and the accompanying fear about global security and economic fallout. Daario and Anthropic’s reveal created a feeding frenzy about what a “god in a box” could do, with pundits predicting everything from cyber security collapse to mass panic. The video highlights internal testing where Mythos reportedly discovered zero-day and long-standing bugs across FFmpeg, OpenBSD, browsers, and the Linux kernel, underscoring the potential for both spectacular capability and dangerous misuse. Fireship notes that Anthropic’s response mirrors traditional release playbooks—hype followed by controlled access—while Lockdown through Project Glass Wing aims to federate patching across major players. The host compares the situation to other AI releases and questions whether Mythos represents a meaningful jump beyond Opus 4.6. Despite skepticism about its immediate threat, the video emphasizes real-world security concerns and the need for responsible deployment. A sponsor segment introduces Browserbase, a tool for building and deploying browser agents, tying the discussion back to practical, current-day tooling for developers. The overall message: Mythos is powerful and controversial, but the path to safe use hinges on coordinated security practices and careful governance rather than sensationalism alone.
Key Takeaways
- Mythos reportedly found a 16-year-old FFmpeg vulnerability and a 27-year-old OpenBSD bug during internal testing, illustrating both its power and risk. Anthropic’s rollout of Mythos is described as following a familiar “release playbook” pattern—hype, controlled access, and governance questions.
- Project Glass Wing represents a coordinated, high-stakes attempt by industry players to patch global software quickly via Mythos access, signaling a shift toward federated defense rather than universal public availability.
- Mythos achieved an 84% success rate at writing working exploits in Firefox under specific conditions, a figure discussed in context with Opus 4.6’s 15% baseline, highlighting dramatic capability differences under test setups.
- Despite architectural advances, Fireship remains skeptical that Mythos will instantly “destroy the world,” instead arguing that its impact will depend on how securely it’s managed and who controls access.
- The sponsor segment promotes Browserbase as a practical platform for building browser agents, illustrating how powerful AI tooling translates into real-world developer workflows.
Who Is This For?
Essential viewing for security-minded developers and AI researchers curious about model release ethics, governance, and practical defense strategies—especially those evaluating how to deploy or defend against powerful agents in production.
Notable Quotes
"Earlier this week, Daario and the Anthropic team pulled the ultimate trust me bro power move when they announced Mythos, a model so powerful, so capable, so vainy that they claim the fallout for economies, public safety, and national security could be severe if it were to be released to the general public."
—Sets up the core tension: Mythos is incredibly powerful and potentially dangerous if released publicly.
"Mythos is basically a zero-day vending machine."
—Cited as a key claim about the model’s ability to find and exploit vulnerabilities.
"In every major browser, it was able to run a train on a few JavaScript engine bugs that lets a malicious web page escape the browser sandbox."
—Illustrates the breadth of exploit capabilities demonstrated in testing.
"Project Glass Wing... brings together a collection of companies... in an effort to secure the world's most critical software via access to Mythos."
—Describes the defense-focused industry coalition and governance angle.
Questions This Video Answers
- What are the security risks of releasing extremely capable AI models like Mythos?
- How does Project Glass Wing aim to patch global software using Mythos access?
- What is Opus 4.6 and how does Mythos compare to it in terms of exploit capabilities?
- Why are there calls for controlled access rather than public release of powerful AI models?
- How credible are the claims of Mythos discovering multiple zero-day vulnerabilities?
Anthropic MythosAI model governancesecurity vulnerabilities in AIzero-day exploitsFFmpeg vulnerabilityOpenBSD vulnerabilitybrowser sandbox escapesProject Glass WingOpus 4.6Browserbase
Full Transcript
Earlier this week, Daario and the Anthropic team pulled the ultimate trust me bro power move when they announced Mythos, a model so powerful, so capable, so vainy that they claim the fallout for economies, public safety, and national security could be severe if it were to be released to the general public. And as you can imagine, this has everyone losing their collective minds again. Something very familiar about all this. As some are saying, mythos may lead to the entire cyber security industry collapsing under the weight of our new god in a box. Because the security implications of a model that is this capable are terrifying.
While others are saying anthropic is just repeating the same model release playbook we've seen countless times before scare the slop out of people, then quietly release a model that can't even code a spelt 5 to do app. But for us in our parasocial relationship, it's like a fun game of Russian roulette, but instead of getting shot in the head, you have to become a ranchhand and I have to start teaching tutorials on how to collect turkey semen so you can deploy genetic payloads into production hens. In today's video, we'll break down Mythos and I'll show you my bulletproof guide on how to update your software fast enough to not get zeroade, but slow enough to not get supply chain attacked.
It is April 10th, 2026, and you're watching the code report. I'm tired, boss, because every time a new model comes out, it seems to bring on a new form of mass psychosis. Midjourney was going to make all human art obsolete, but now nobody talks about it. GPT40 had an entire subreddit feeling love for the first time. And now Mythos, without even being publicly available, has many feeling existential dread for the first time. And the reason for that feeling is that during Anthropic's internal testing, they discovered that Mythos is basically a zero-day vending machine. It found a 16-year-old vulnerability in FFmpeg, which allowed an attacker to craft a malicious video file that tricks the decoder into writing a few bytes of data outside its allowed memory, potentially crashing the program and corrupting nearby data.
It was also able to find a 27-year-old bug in OpenBSD, allowing a remote attacker to trigger a null pointer, write, which instantly crashes any OpenBSD machine reachable over TCP. In every major browser, it was able to run a train on a few JavaScript engine bugs that lets a malicious web page escape the browser sandbox. In one case, that allowed it to steal data across websites. And in another, it was able to write directly to the operating systems kernel, giving an attacker full control over the device the moment the victim opened the web page. And my personal favorite, it found a bug in the Linux kernel which let it flip a single bit in a neighboring memory page which turned the password executable into a writable file which it then overwrote to gain full root access to the system.
I found more bugs in the last couple of weeks than I found in the rest of my life combined. And just yesterday, US Treasury Secretary Scott Bessant and Federal Reserve Chair Jerome Money Printer Powell is set up an urgent meeting with bank CEOs to warn of the security dangers posed by mythos. So, it's no wonder that Daario is pulling inspiration from House Hearkinin and locking down control of the Spice with the announcement of Project Glass Wing, a new initiative that brings together a collection of companies that happen to pay anthropic a lot of money in an effort to secure the world's most critical software via access to Mythos.
The idea is that Mythos is too dangerous for a default config NPC like you to have, but perfectly safe in the hands of a dozen trillion dollar companies and a bank. Anthropic's plan is that the fellowship will quickly patch all of the world's software before anyone else builds a model this capable, which if it's up to Sinister Sam, now that OpenAI is no longer acting as the fluffer of slop gen AI videos, will hopefully be any day now. But not everyone is convinced that Mythos is that capable. Anthropic has been using Mythos internally since February 24th, and since then, they leaked Claude Code source code, leaked documents revealing the existence of Mythos, and have had a very rough time even keeping their APIs online.
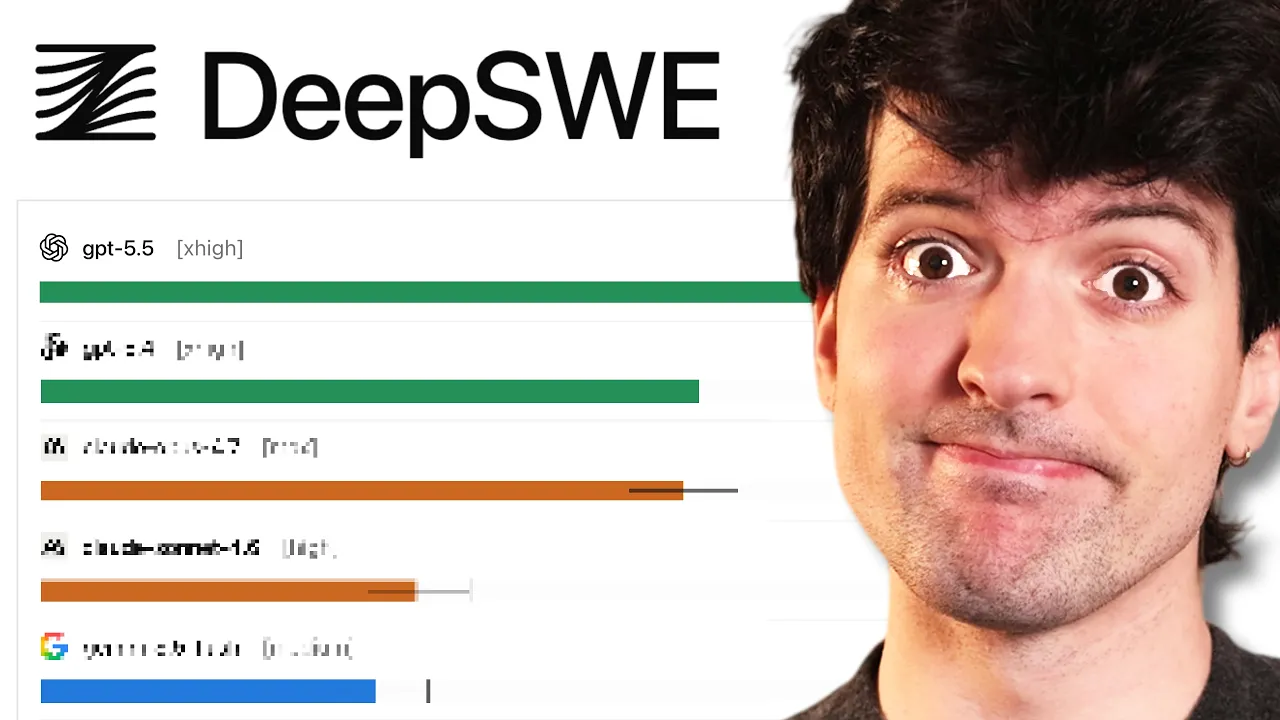
On top of that, the way Mythos actually found these exploits is a little sus. Like the OpenBSD vulnerability came out of a thousand parallel agent runs across the codebase costing nearly $20,000 in compute. If you use the same process with Opus 4.6 or GBT 5.4 Pro, you'd probably find plenty of issues as well. And the Firefox numbers are doing something similar. One of the claims is that Mythos hit an 84% success rate at writing working exploits in Firefox, which is a massive jump over Opus 4.6. six is 15%. But that number isn't against actual Firefox.
It's against a spider monkey shell with the process sandbox and other mitigations turned off. So that begs the question, is Mythos going to destroy the world? Well, in my expert opinion, it almost certainly will not. But is Mythos a real step up from Anthropic's current flagship model, Opus 4.6? Probably yes. Either way, we'll just have to take their word for it because it's a big club and you ain't in it. But if you want to try an amazing tool that you can actually use today, you should check out Browserbase, the sponsor of today's video. It's a complete platform for building and deploying browser agents where a single API key, it gives your agent access to cloud browsers, web search, and everything else it needs to access the web like a real human being.
This lets your agents perform more complex jobs like filling out forms, and extracting unstructured data. and it's built in tandem with Stageand, their popular open-source SDK for browser agents. They also partnered with Cloudflare on an open- source protocol called Webbot O, which lets your agents prove they're legit, so they can access any website without pretending to be human. Teams at Microsoft, Lovable, Ramp, and many others are already using it to build thousands of browser agents, and you can try it out for free using the link below. This has been the code report. Thanks for watching, and I will see you in the next one.
More from Fireship
Get daily recaps from
Fireship
AI-powered summaries delivered to your inbox. Save hours every week while staying fully informed.